Cryptography for Developers (and Everyone Else)
Cryptography for Developers (and Everyone Else): The Invisible Technology That Protects Your Digital Life
Every time you browse a website, send a WhatsApp message, or pay for something online, a powerful invisible shield is protecting you. This shield is cryptography , the science of securing communication in a world where everything travels through public networks.
Most people never see it.
Most developers use it without understanding it.
But everyone relies on it.
Let’s break it down simply, practically, and from a developer’s point of view.
🔐 What Exactly Is Cryptography?
Cryptography is a collection of mathematical techniques that protect data from being read or modified by unauthorized people.

It ensures three things:
- Confidentiality — only the intended person can read the data.
- Integrity — the data hasn’t been tampered with.
- Authentication — you know who the sender really is.
In simple terms: cryptography keeps your digital world safe.
🌍 Why You Already Use Cryptography Every Day
Even if you’re not a developer:
- Every HTTPS website uses cryptography
- Every online payment uses cryptography
- Every WhatsApp message uses end-to-end encryption
- Your passwords are stored using cryptographic hashing
- Software updates are verified with digital signatures
Cryptography is not optional — it’s everywhere.
⚡ The Three Pillars of Modern Cryptography
1️⃣ Symmetric Encryption (Fast, 1 Key)

One secret key encrypts and decrypts the data.
- Algorithms: AES, DES
- Fast → good for encrypting large data
- Used in: disk encryption, HTTPS session data, cloud storage
Example:
AES encrypts your data when you store it in a database or when two systems exchange large JSON payloads.
2️⃣ Asymmetric Encryption (Public & Private Keys)

Two keys:
- Public key → shared openly
- Private key → kept secret
Depending on the purpose, we use them in different directions:
Algorithms: RSA, ECC, Diffie-Hellman
Used in HTTPS, JWT signing, certificates, secure email, SSH.
3️⃣ Hashing (One-Way Fingerprint)

A hash takes data and produces a fixed-length output.
It cannot be reversed.
Algorithms: SHA-256, SHA-3
Used for:
- Password storage
- File integrity checks
- Blockchain
- API signatures
One small change → completely different hash (avalanche effect).
🔑 HMAC: Message Authentication Code (Hash + Secret Key)
HMAC ensures integrity + authenticity using a hash function + secret key.
Used in:
- API request signing (Stripe, AWS, Twilio)
- JWT HS256 tokens
- Webhooks
- Internal service-to-service communication
If the message or signature is modified, HMAC fails instantly.
✍️ Digital Signatures
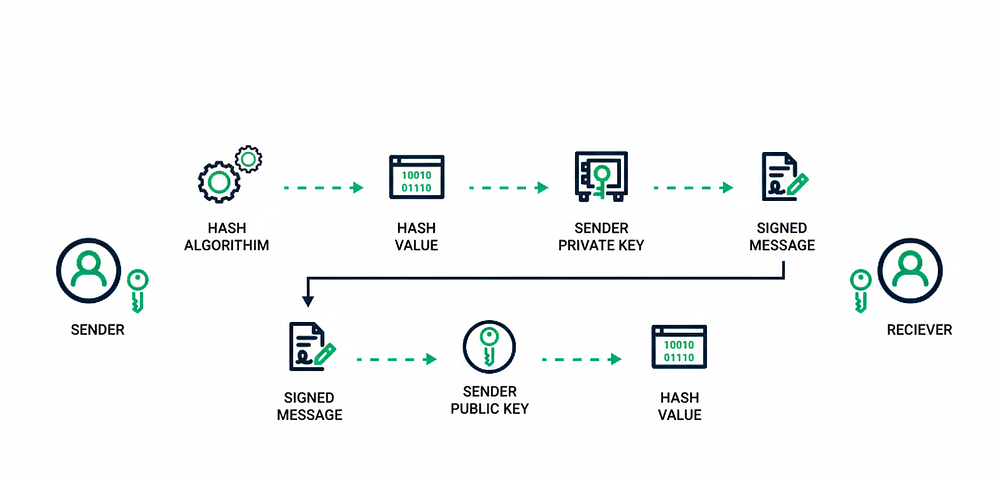
A digital signature proves:
- Who sent the message (authenticity)
- The message wasn’t tampered with (integrity)
Process:
- Hash the message
- Encrypt the hash with sender’s private key → signature
- Receiver verifies using sender’s public key
Used in:
- Software signing
- Blockchain transactions
- Legal documents
- Email (DKIM)
🌐 How HTTPS Actually Works (Super Simple Explanation)
Most people think HTTPS = encryption.
But it’s actually multiple cryptographic systems working together:

Step 1 — Asymmetric encryption
- Browser → server
- Server sends SSL certificate containing its public key
- Browser verifies certificate authority (CA)
Step 2 — Key Exchange
- Browser generates a symmetric key
- Encrypts it with server’s public key → sends
- Server decrypts using its private key
Now both have the same symmetric key.
Step 3 — Symmetric encryption
All communication now uses AES (fast!) for actual data transfer.
Step 4 — Integrity checks
HTTPS uses SHA-based MACs to ensure data isn’t modified.
➡️ HTTPS = asymmetric (for identity) + symmetric (for speed) + hashing (for integrity)
🧑💻 Real Developer Use Cases
Here’s how cryptography appears in real life:
Symmetric Encryption (AES)
- Encrypting sensitive database fields
- Securely storing access tokens
- Mobile apps protecting local storage
Asymmetric Encryption
- Verifying JWT tokens (RS256)
- SSH keys
- SSL certificates
- Email encryption (PGP)
Hashing (SHA-256)
- Password hashing (with salt + slow hash like bcrypt/argon2)
- File checksum validation
- Blockchain mining
HMAC
- Stripe or PayPal webhook validation
- AWS Signature V4
- API request signing
Digital Signatures
- Software updates
- PDF signing
- Smart contracts
- Blockchain transactions
✅ Best Practices for Developers
- Never build your own crypto algorithm
- Use well-tested libraries (OpenSSL, libsodium, crypto-js)
- Use AES-256 for symmetric encryption
- Use RSA-2048 or ECC for asymmetric
- Hash passwords with bcrypt, Argon2, or scrypt — not SHA-256
- Keep private keys protected (KMS, Vault, HSMs)
- Use HTTPS everywhere
🧠 Final Thoughts
Cryptography isn’t just for security experts.
It’s the foundation of trust on the internet.
Whether you’re writing backend APIs, building mobile apps, developing fintech systems, or simply browsing the web — you’re relying on cryptography every single day.
Understanding these concepts makes you a better developer and a more informed digital citizen.